I’m pretty new to selfhosting and homelabs, and I would appreciate a simple-worded explanation here. Details are always welcome!
So, I have a home network with a dynamic external IP address. I already have my Synology NAS exposed to the Internet with DDNS - this was done using the interface, so didn’t require much technical knowledge.
Now, I would like to add another server (currently testing with Raspberry Pi) in the same LAN that would also be externally reachable, either through a subdomain (preferable), or through specific ports. How do I go about it?
P.S. Apparently, what I’ve tried on the router does work, it’s just that my NAS was sitting in the DMZ. Now it works!
Welcome to the wonderful world of reverse proxies!
You need a reserve proxy. That’s a piece of software that takes the requests and puts them toward the correct endpoint.
You need to create port forwards in the router and direct 80 and 443 (or whatever you’re using) toward the host of the reverse proxy and that is listening to on those ports. If it recognized the requests are for nas.your.domain, it will forward the requests to the NAS.
Common reverse proxies are nginx or caddy. You can install it on your raspberry, it doesn’t need it’s own device.
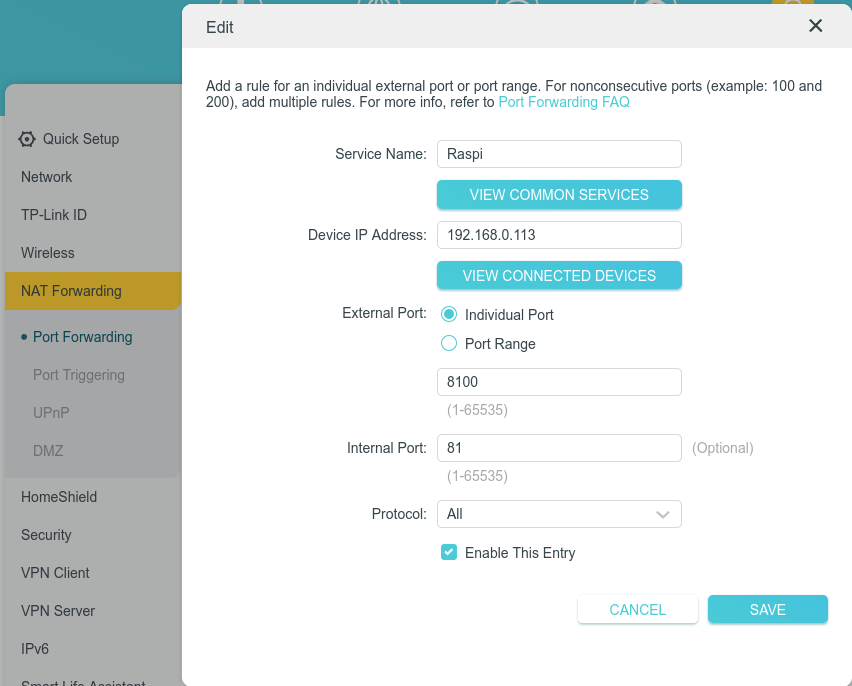
If you don’t want that, you can create different port forwards on your router (e.g. 8080 and 8443 to the Raspi) and configure your service on the Raspi corresponding. But it doesn’t scale well and you’d need to call everything with the port and the reverse proxy is the usual solution.
There’s an issue with that first part. Do I configure it right? Should <domain>:8100 be redirected to 192.168.0.113:81 in this case?
External 80 to internal 80 and external 443 to internal 443
With this config you don’t have to deal with ports later, as http is 80, https is 443 by default.
If you run some container on port 81, you have to deal with that in the reverse proxy, not in the router. E.g. redirect something.domian.tld to 192.168.0.103:81
If you use docker check out nginxproxymanager, it has a very beginner friendly admin webui. You shouldn’t forward the admin ui’s port, you need to access it only from your lan.
What are you running?
If it is http based use a reverse proxy like Caddy
Update: tried Caddy, love it, dead simple, super fast, and absolutely works!
Did you also forward UDP port 443?
If not I would as well since it is used for QUIC which is supported and automatically turned on for Caddy.
I really feel like people who are beginners shouldnt play with exposing their services. When you set up Caddy or some other reverse proxy and actually monitor it with something like fail2ban you can see that the crawlers etc are pretty fast to find your services. If any user has a very poor password (or is reusing a leaked one) then someone has pretty open access to their stuff and you wont even notice unless you’re logging stuff.
Of course you can set up 2FA etc but that’s pretty involved compared to a simple wg tunnel that lives on your router.
VPN is definitely the way to go for home networks. Your router even has one built in. OpenVPN and Wireguard are good.
If you really want to expose stuff like this the proper way is to isolate your home network from your internet exposed network using a VLAN. Then use a reverse proxy, like caddy and place everything behind it.
Another benefit of a reverse proxy is you don’t need to setup https certs on everything just the proxy.
You do need a business or prosumer router for this though. Something like Firewalla or setting up a OpenWRT or OPNsense.
Synology also has there quick connect service as well. While not great if you keep UPNP off and ensure your firewall and login rate limiting is turned on it may be better then just directly exposing stuff. But its had its fair share of problems so yeah.
Consider not self hosting everything. For example if all your family cares about is private photo storage, consider using a open source E2EE encrypted service for photos on the cloud like Ente Photos. Then you can use VPN for the rest. https://www.privacyguides.org/ has some recommendations for privacy friendly stuff.
Also consider the fallout that would happen if you are hacked. If all your photos and other things get leaked because your setup was not secure was it really any better than using big tech?
If nothing else please tell me you are using properly setup https certs from Let’s Encrypt or another good CA. Using a firewall and have login rate limiting setup on everything that is exposed. You can also test your SSL setup using something like https://www.ssllabs.com/ssltest/
No truly private photos ever enter the NAS, so on that front it should be fine.
VPN is not an option for several reasons, unfortunately.
But I do have a Let’s Encrypt certificate, firewall and I ban IP after 5 unsuccessful login attempts. I also have SSH disabled completely.
SSL Test gave me a rating of A
Who is externally reaching these servers?
Joe public? Or just you and people you trust?If it’s Joe public, I wouldn’t have the entry point on my home network (I might VPS tunnel, or just VPS host it).
If it’s just me and people I trust, I would use VPN for access, as opposed to exposing all these services publicly
Your stuff is more likely to get scanned sitting in a VPS with no firewall than behind a firewall on a home network
Why wouldn’t you setup a firewall on the VPS?
all home routers have NAT which functions as a firewall, but VPSes don’t cone with any firewall by default, so you’d have to set one up. Also VPS ranges seem to hotter for scanning.
You don’t need NAT for a Firewall. NAT doesn’t provide any security benefits what so ever.
If you put something on the internet it should always have a Firewall. Use either ufw or firewalld. I don’t see your argument since anything the bots can each will get probed.


